SonarQube SonarScanner reference
You can set up a Security step with SonarQube SonarScanner to analyze your code repos and ensure that they are secure, reliable, readable, and modular, among other key attributes.
- STO supports repository scanning only for SonarScanner.
- STO supports all languages supported by SonarScanner.
- Before you scan your repo, make sure that you perform any prerequisites for the language used in your repo. If you are scanning a Java repo with more than one Java file, for example, you must compile
.classfiles before you run the scan.
Go to the SonarQube language reference for details about specific language requirements.
SonarQube step configuration
The recommended workflow is add a SonarQube step to a Security Tests or CI Build stage and then configure it as described below. You can also configure SonarQube scans programmatically by copying, pasting, and editing the YAML definition.
- UI configuration support is currently limited to the following scanners: Aqua Trivy, Bandit, Black Duck, Checkmarx, Grype, Mend, Prisma Cloud, Snyk, SonarQube, and ZAP.
- Each step palette shows only the options that apply to a specific scan. If you're setting up a repository scan, for example, the UI won't show Container Image settings.
- Docker-in-Docker is not required for these steps unless you're scanning a container image. If you're scanning a repository using Bandit, for example, you don't need to set up a Background step running DinD.
- Support is currently limited to Kubernetes and Harness Cloud AMD64 build infrastructures only.
Step Palette
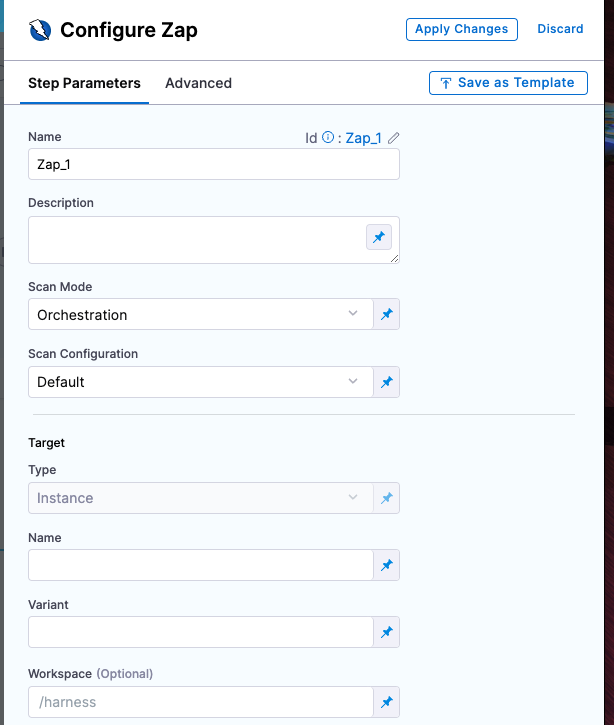
Scan
Scan Mode
The orchestration mode to use for the scan. The following list includes the UI and YAML values for the supported options.
- Orchestrated A fully-orchestrated scan. A Security step in the Harness pipeline orchestrates a scan and then normalizes and compresses the results.
- Extraction A partially-orchestrated scan. The Security step pulls scan results from an external SaaS service and then normalizes and compresses the data.
- Ingestion Ingestion scans are not orchestrated. The Security step ingest results from a previous scan (for a scan run in an previous step) and then normallizes and compresses the results.
Scan Configuration
The predefined configuration to use for the scan. All scan steps have at least one configuration.
Target
Type
- Repository Scan a codebase repo.
Name
The Identifier that you want to assign to the target you’re scanning in the pipeline. Use a unique, descriptive name such as codebaseAlpha or jsmith/myalphaservice.
Variant
An identifier for a specific target to scan, such as the branch name or image tag. This identifier is used to differentiate or group results for a target. Harness maintains a historical trend for each variant.
Workspace
The workspace path on the pod running the Security step. The workspace path is /harness by default.
You can override this if you want to scan only a subset of the workspace. For example, suppose the pipeline publishes artifacts to a subfolder /tmp/artifacts and you want to scan these artifacts only. In this case, you can specify the workspace path as /harness/tmp/artifacts.
Ingestion File
The results data file to use when running an Ingestion scan. Generally an Ingestion scan consists of a scan step (to generate the data file) and an ingestion step (to ingest the data file).
Authentication
Domain (extraction)
The fully-qualified URL to the scanner.
Enforce SSL
The step and the scanner communicate over SSL by default. Set this to false to disable SSL (not safe).
Access Token
The access token to log in to the scanner. In most cases this is a password or an API key.
You should create a Harness text secret with your encrypted token and reference the secret using the format <+secrets.getValue(project.container-access-id>. For more information, go to Add and Reference Text Secrets.
Scan Tool
Include
The initial scope for the scan. This should match the format required by the scanner.
Java Libraries
A comma-separated list of paths to files with third-party libraries used by your tests. If you’re running a SonarQube scan, for example, this corresponds to the sonar.java.libraries parameter.
Java Binaries
A comma-separated list of paths to the folders with the bytecode files you want to scan. If you’re running a SonarQube scan, for example, this corresponds to the sonar.java.binaries parameter.
Log Level, CLI flags, and Fail on Severity
Log Level
The minimum severity of the messages you want to include in your scan logs. You can specify one of the following:
- DEBUG
- INFO
- WARNING
- ERROR
Additional CLI flags
You can use this field to customize the scan with specific command-line arguments supported by that scanner.
Fail on Severity
Every Security step has a Fail on Severity setting. If the scan finds any vulnerability with the specified severity level or higher, the pipeline fails automatically. You can specify one of the following:
CRITICALHIGHMEDIUMLOWINFONONE— Do not fail on severity
The YAML definition looks like this: fail_on_severity : critical # | high | medium | low | info | none
Settings
You can add a tool_args setting to run the sonar-scanner binary with specific command-line arguments. For example, suppose the scan is experiencing timeouts due to long response times from a web service. You can increase the timeout window like this: tool_args = -sonar.ws.timeout 300.
Additional Configuration
In the Additional Configuration settings, you can use the following options:
Advanced settings
In the Advanced settings, you can use the following options:
Security step configuration (deprecated)
Set up a SonarQube scan in a Security step
You can set up a Security step with SonarQube SonarScanner to analyze your code repos and ensure that they are secure, reliable, readable, and modular, among other key attributes.
Scan types
STO supports the following scan types for SonarQube:
orchestratedScan— A Security step in the pipeline runs the scan and ingests the results. This is the easiest to set up and supports scans with default or predefined settings.dataLoad— The pipeline downloads scan results using the SonarScanner API.ingestionOnly— Run the scan in a Run step, or outside the pipeline, and then ingest the results. This is useful for advanced workflows that address specific security needs. See Ingest scan results into an STO pipeline.
Required settings
product_name=sonarqubescan_type=repositoryproduct_config_name=default— Runs a SonarQube scan with default settings.policy_type— Enter one of the following:orchestratedScan— A Security step in the pipeline runs the scan and ingests the results. This is the easiest to set up and supports scans with default or predefined settings.dataLoad— The pipeline downloads scan results using the SonarScanner API.ingestionOnly— Run the scan in a Run step, or outside the pipeline, and then ingest the results. This is useful for advanced workflows that address specific security needs. See Ingest scan results into an STO pipeline.
repository_project— The repository name. If you want to scanhttps://github.com/my-github-account/codebaseAlpha, for example, you would set this tocodebaseAlpha.repository_branch— The git branch to scan. You can specify a hardcoded string or use the runtime variable<+codebase.branch>. This sets the branch based on the user input or trigger payload at runtime.fail_on_severity- See Fail on Severity.
ingestionOnly settings
Ingestion scan settings
The following settings are required for Security steps where the policy_type is ingestionOnly.
target nameThe Identifier that you want to assign to the target you’re scanning in the pipeline. Use a unique, descriptive name such as codebaseAlpha or jsmith/myalphaservice.variantAn identifier for a specific target to scan, such as the branch name or image tag. This identifier is used to differentiate or group results for a target. Harness maintains a historical trend for each variant.ingestion_fileThe results data file to use when running an Ingestion scan. You should specify the full path to the data file in your workspace, such as/shared/customer_artifacts/my_scan_results.json.
The following steps outline the general workflow for ingesting scan data into your pipeline:
Specify a shared folder for your scan results, such as
/shared/customer_artifacts. You can do this in the Overview tab of the Security stage where you're ingesting your data.Create a Run step that copies your scan results to the shared folder. You can run your scan externally, before you run the build, or set up the Run step to run the scan and then copy the results.
Add a Security step after the Run step and add the
target name,variant, andingestion_filesettings as described above.
For a complete workflow description and example, go to Ingest Scan Results into an STO Pipeline.
orchestratedScan and dataLoad settings
product_domain— The URL of the SonarQube server.product_access_token— The access token to communicate with the SonarQube server. You must create a secret for the token and use the format<+secrets.getValue("secret_name")>to reference the secret. This example references a secret created at the project level. For additional details on referencing secrets, go to Add and Reference Text Secrets.
Go to the SonarQube docs for information about creating tokens.product_project_name—The name of the SonarQube project. This is the also the target name in the Harness UI (Security Tests > Test Targets).product_project_key— The unique identifier of the SonarQube project you want to scan. Look forsonar.projectKeyin the sonar-project.properties file.product_exclude— If you want to exclude some files from a scan, you can set the sonar.exclusions key in your SonarQube project. See Narrowing the Focus in the SonarQube docs.product_java_binaries— When scanning Java, you need to set thesonar.java.binarieskey in SonarQube. This is a list of comma-separated paths with the compiled bytecode that correspond to your source files. See Java in the SonarQube docs.product_java_libraries—sonar.java.binariesis a comma-separated list of paths to files with third-party libraries (JAR or Zip files) used by your project. See Java in the SonarQube docs.
YAML configuration
The following YAML pipeline includes example stages for scanning a repository (Bandit step), an image (AquaTrivy step), and an app (ZAP step).
If you want to set up scan steps programmatically using YAML, the best practice is to set up your step in a pipeline using the Visual Editor and then copy, paste, and edit the YAML definition.
pipeline:
name: sto-step-palette-example
identifier: stosteppaletteexample
projectIdentifier: my_sto_project
orgIdentifier: default
tags: {}
properties:
ci:
codebase:
connectorRef: MY_GITHUB_CONNECTOR
build: <+input>
stages:
- stage:
name: runSecurityTestsStage
identifier: runSecurityTestsStage
type: SecurityTests
spec:
cloneCodebase: true
execution:
steps:
- step:
type: Background
name: docker_dind
identifier: Background_1
spec:
connectorRef: MY_DOCKER_CONNECTOR
image: docker:dind
shell: Sh
privileged: true
- step:
type: Bandit
name: banditScanRepo
identifier: banditScanRepo
spec:
mode: orchestration
config: default
target:
name: dvpwa
type: repository
variant: <+codebase.branch>
advanced:
log:
level: info
fail_on_severity: none
- step:
type: AquaTrivy
name: aquaTrivyScanContainerImage
identifier: aquaTrivyScanContainerImage
spec:
mode: orchestration
config: default
target:
name: myAlphaService
type: container
variant: latest
advanced:
log:
level: info
privileged: true
image:
type: docker_v2
name: jsmith/myalphaservice
domain: docker.io
tag: latest
- step:
type: Zap
name: zapScanInstance
identifier: zapScanInstance
spec:
mode: orchestration
config: default
target:
name: my-gruyere
type: instance
variant: test
advanced:
log:
level: info
instance:
domain: https://google-gruyere.appspot.com/XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX/
protocol: https
infrastructure:
type: KubernetesDirect
spec:
connectorRef: MY_K8S_CONNECTOR
namespace: harness-delegate-ng
automountServiceAccountToken: true
nodeSelector: {}
os: Linux
sharedPaths:
- /var/run